Why choose us
Reliable infrastructure and expert support you can depend on
Measurably better infra
As reported by our customers
24/7 on call
Prompt incident response
Continuous Monitoring & Alerting
Proactive detection minimizes impact
Security-first
Robust key management and access controls, SOC2 ready
5+ years experience
In specialized blockchain infrastructure operations
High availability
Fault-tolerant, multi-region systems
Why choose us
Reliable infrastructure and expert support you can depend on
Measurably better infra
As reported by our customers
24/7 on call
Prompt incident response
Continuous Monitoring & Alerting
Proactive detection minimizes impact
Security-first
Robust key management and access controls, SOC2 ready
5+ years experience
In specialized blockchain infrastructure operations
High availability
Fault-tolerant, multi-region systems
Why choose us
Reliable infrastructure and expert support you can depend on
Measurably better infra
As reported by our customers
24/7 on call
Prompt incident response
Continuous Monitoring & Alerting
Proactive detection minimizes impact
Security-first
Robust key management and access controls, SOC2 ready
5+ years experience
In specialized blockchain infrastructure operations
High availability
Fault-tolerant, multi-region systems
Why choose us
Reliable infrastructure and expert support you can depend on
Measurably better infra
As reported by our customers
24/7 on call
Prompt incident response
Continuous Monitoring & Alerting
Proactive detection minimizes impact
Security-first
Robust key management and access controls, SOC2 ready
5+ years experience
In specialized blockchain infrastructure operations
High availability
Fault-tolerant, multi-region systems
Security Standards
Fault-tolerant systems built for predictable operation and continuous availability


SOC2 ready
SOC2 ready
We are strictly adhering to SOC2 standards, and are currently in the process of getting our certification.

Defense
Defense
Defense-in-depth across all system layers. MPC-based signing and industry-standard key management, secure signing workflows.

Redundancy
Redundancy
Redundant geographic deployments with hot failover ensure deterministic behavior during network or platform events.

Access Control
Access Control
Least-privilege access controls, encrypted end-to-end communications, and VPN-based isolation protect all components.
Research & News

Ethereum: Fusaka Upgrade | Multi-Level Ethereum Scaling
Ethereum: Fusaka Upgrade | Multi-Level Ethereum Scaling
Ethereum: Fusaka Upgrade | Multi-Level Ethereum Scaling

Monad Starter Kit – Exploring The Monad Ecosystem
Monad Starter Kit – Exploring The Monad Ecosystem
Monad Starter Kit – Exploring The Monad Ecosystem
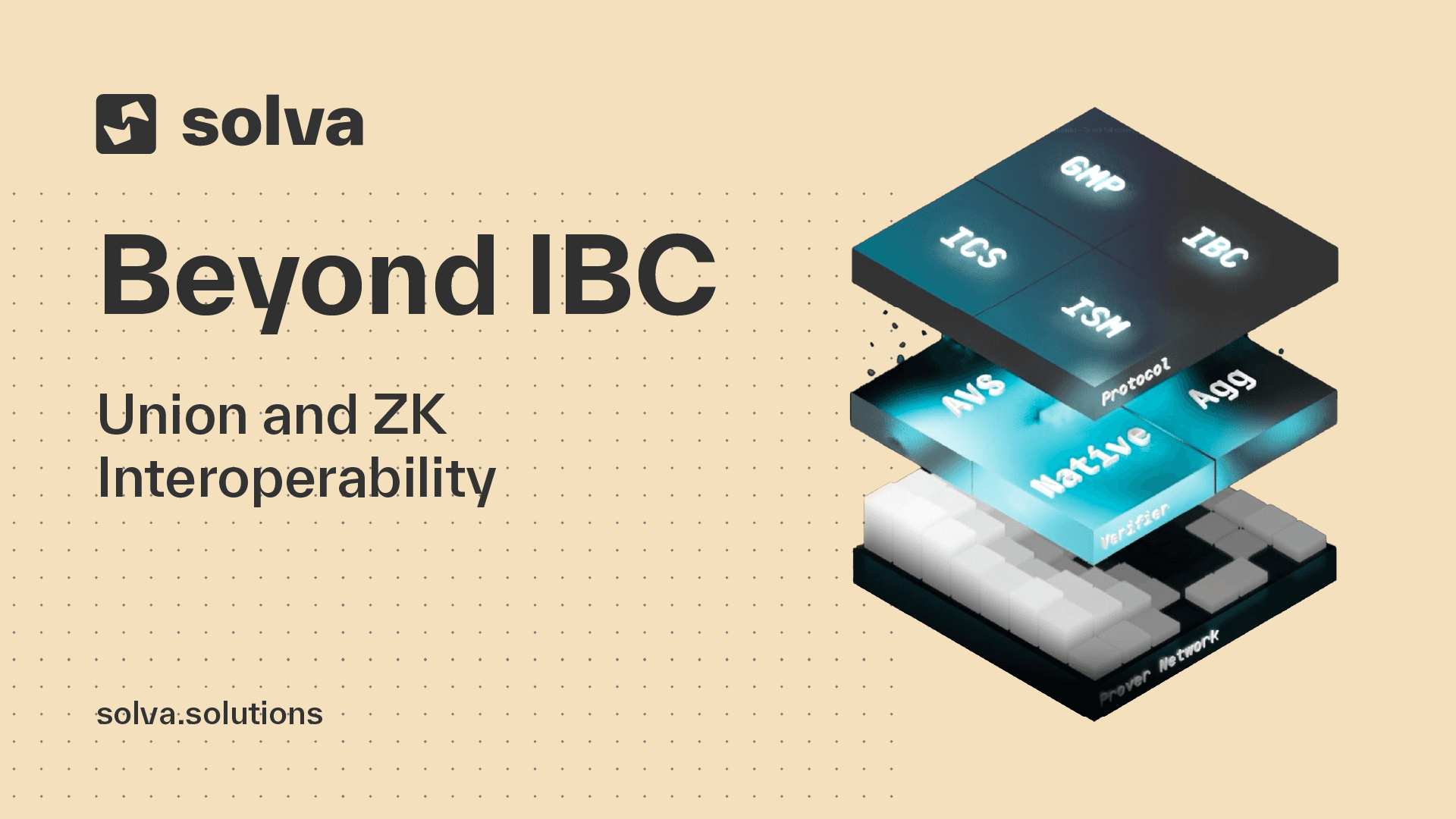
Beyond IBC: Union and ZK Interoperability
Beyond IBC: Union and ZK Interoperability
Beyond IBC: Union and ZK Interoperability
Staking
Supported Networks
Yield Optimization
COMING SOON
Referral Program
Customized Staking
Ethereum DVT Staking
Solana Network Operations
Babylon BTC Staking
Products
Institutional Staking
White-Label Validator
Appchain Development
Cross-Chain Relayers
Managed Nodes / RPCs
Trading Infrastructure
COMING SOON
Monitoring Tools
Company
About Solva
Brand Kit
COMING SOON
Ventures & Partners
Contact
Imprint
Terms & Conditions
Privacy Policy
SOC2

Staking
Supported Networks
Yield Optimization
COMING SOON
Referral Program
Customized Staking
Ethereum DVT Staking
Solana Network Operations
Babylon BTC Staking
Products
Institutional Staking
White-Label Validator
Appchain Development
Cross-Chain Relayers
Managed Nodes / RPCs
Trading Infrastructure
COMING SOON
Monitoring Tools
Company
About Solva
Brand Kit
COMING SOON
Ventures & Partners
Contact
Imprint
Terms & Conditions
Privacy Policy
SOC2

Staking
Supported Networks
Yield Optimization
COMING SOON
Referral Program
Customized Staking
Ethereum DVT Staking
Solana Network Operations
Babylon BTC Staking
Products
Institutional Staking
White-Label Validator
Appchain Development
Cross-Chain Relayers
Managed Nodes / RPCs
Trading Infrastructure
COMING SOON
Monitoring Tools
Company
About Solva
Brand Kit
COMING SOON
Ventures & Partners
Contact
Imprint
Terms & Conditions
Privacy Policy
SOC2

Staking
Supported Networks
Yield Optimization
COMING SOON
Referral Program
Customized Staking
Ethereum DVT Staking
Solana Network Operations
Babylon BTC Staking
Products
Institutional Staking
White-Label Validator
Appchain Development
Cross-Chain Relayers
Managed Nodes / RPCs
Trading Infrastructure
COMING SOON
Monitoring Tools
Company
About Solva
Brand Kit
COMING SOON
Ventures & Partners
Contact
Imprint
Terms & Conditions
Privacy Policy
SOC2





